Frequently Asked Questions
When a kubernetes environment has everything it needs to serve traffic to real end users without human assistance, we consider it "production-ready."
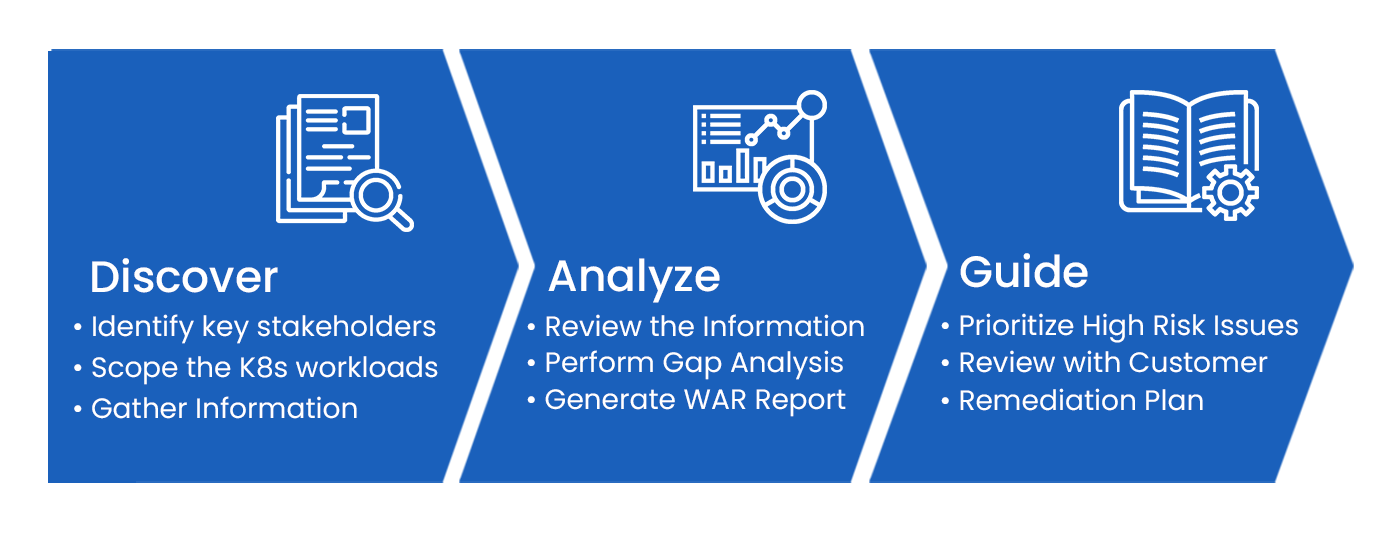
A comprehensive assessment or evaluation of various components of kubernetes architecture, such as Scalability, Resource Management, Health Checks, Rollout & Rollback, Monitor & Log, Security, Configuration Management, Graceful Shutdown, and Backup & Disaster Recovery, allows you to identify misconfigurations within your system and remediation of that allows you achieve desired Kubernetes state.